Introduction
HackenProof is a leading corporate bug bounty platform that connects organizations with cybersecurity experts and ethical hackers to help them identify and address vulnerabilities in their systems and applications. While KYC (Know Your Customer) is a common requirement in many financial and regulated industries to verify the identity of customers, it may not necessarily be required on a platform like HackenProof, which focuses on cybersecurity services.
At the same time, we at HackenProof understand how KYC is essential nowadays, and we offer the option for customers to perform KYC checks on researchers who participate in their bug bounty programs using HackenProof’s KYC providers.
Whether KYC is optional or mandatory on HackenProof depends on customers’ specific policies and requirements. So, our customers can skip our KYC function and use their own KYC process and providers
The importance of KYC for businesses
KYC is important for companies for several critical reasons:
- meet legal requirements
- reduce risks related to payment processing
- prevent fraud
- enhance their reputation
- make informed business decisions
The KYC approach can help establish trust and credibility within the cybersecurity community and ensure that the researchers using the platform are legitimate and meet certain identity verification criteria.
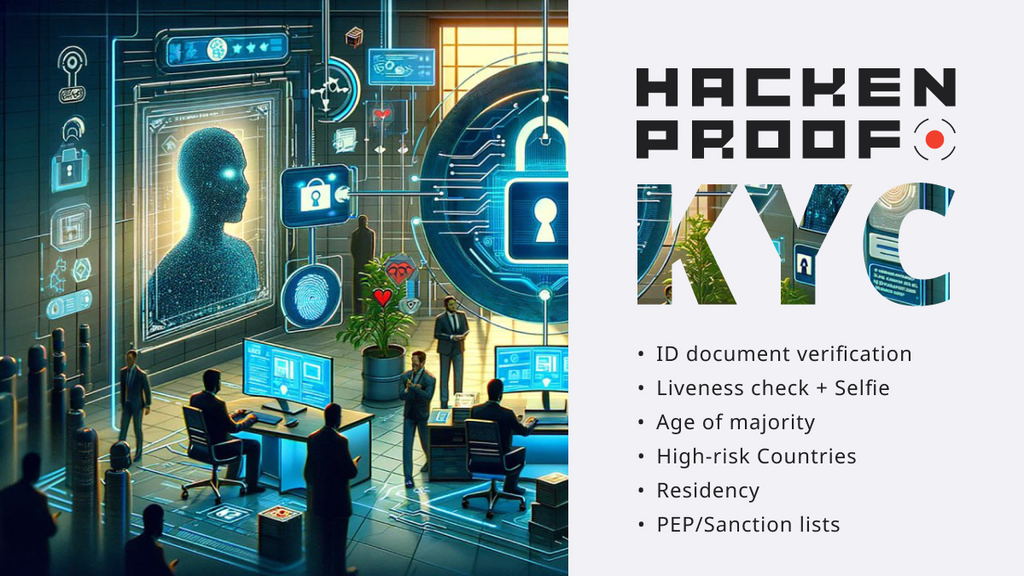
What HackenProof KYC includes
HackenPorof supports different levels of verification. Additionally, each level may be extended. This will impact the data the user is requested to share and consequently their journey.
The primary KYC level (requested by default) includes:
- ID document verification: collection and validation of ID documents through OCR technology.
- Liveness check: Automatic liveness detection and automatic face-match.
- Selfie: Identity verification through ID document scan and selfie with ID document.
- Age of majority: rejection of Users under 18 years old.
- High-risk Countries: rejection of Users residing in countries included in the European Commission’s list of high-risk third countries and in the FATF monitored and call-for-action lists.
Extra KYC level (under additional request from the customer) includes:
- Residency: collection and verification of proof of address document/country.
- PEP/Sanction lists: rejection of Users that are politically exposed persons (PEPs) or covered by any sanction list
Who holds KYC data
KYC processes typically involve collecting and verifying information during the onboarding and periodically updating this information. HackenProof partners with two KYC service providers, specifically AMLBot, to manage and securely store user KYC data. More detailed information might be provided at the customer’s request.
Both the KYC providers have implemented robust security measures to ensure the safe storage of user KYC data and secure processes while communicating with the HackenProof interface.
Verify if a hacker has passed KYC
At HackenProof, every researcher who successfully completes the KYC process is awarded a specific label.
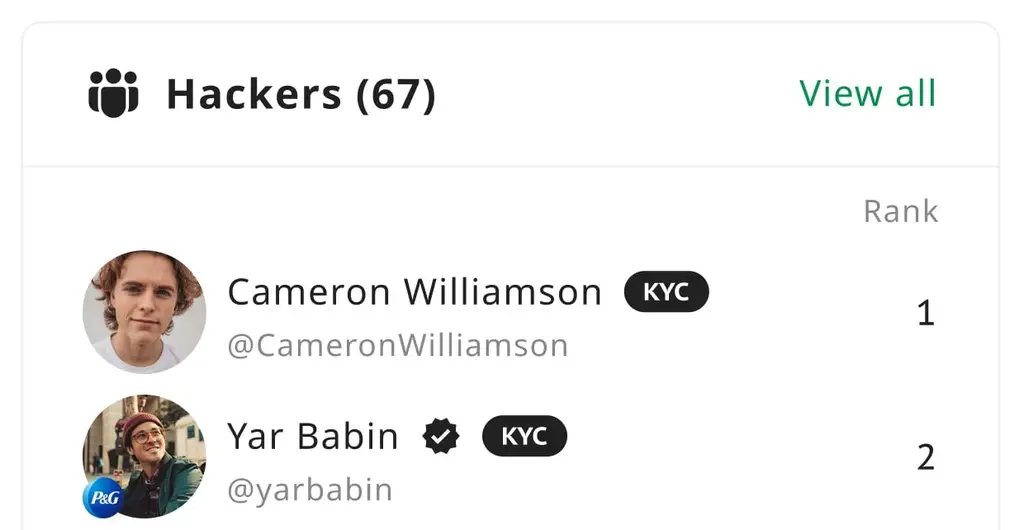
This KYC label is visible on the researcher’s public profile, which is accessible by clicking on the researcher’s username. Also, you can see it by opening the report they submitted, where the label is displayed next to the researcher’s nickname.
The presence of the KYC label indicates that the researcher has successfully passed the primary level of KYC, as mentioned above.
Summary and Key Takeaways
KYC plays a vital role for businesses in cybersecurity, especially in dealing with researchers and managing payments. Utilizing HackenProof’s KYC process enables companies to:
- Mitigate payment processing risks.
- Increase efficiency by eliminating the need for you and your legal department to go through the entire KYC process.
- Achieve cost savings by bypassing third-party KYC providers
- Minimize the risks associated with handling researchers’ sensitive information
- Ensure compliance with data privacy and financial regulations
- Decline payments for researchers from sanctioned countries
- Establish trust between researchers and the platform.
Request a demo call
Want to know more about a comprehensive approach to security and bug bounty programs? Get in touch to request a demo with our team today!

