MythX is a fully automatic scanner for security vulnerabilities in Ethereum and other EVM-based blockchain smart contracts. MythX has a comprehensive range of analysis techniques, such as static analysis, dynamic analysis, and symbolic execution. This can effectively detect security flaws and provide an in-depth analysis report.
How to install MythX
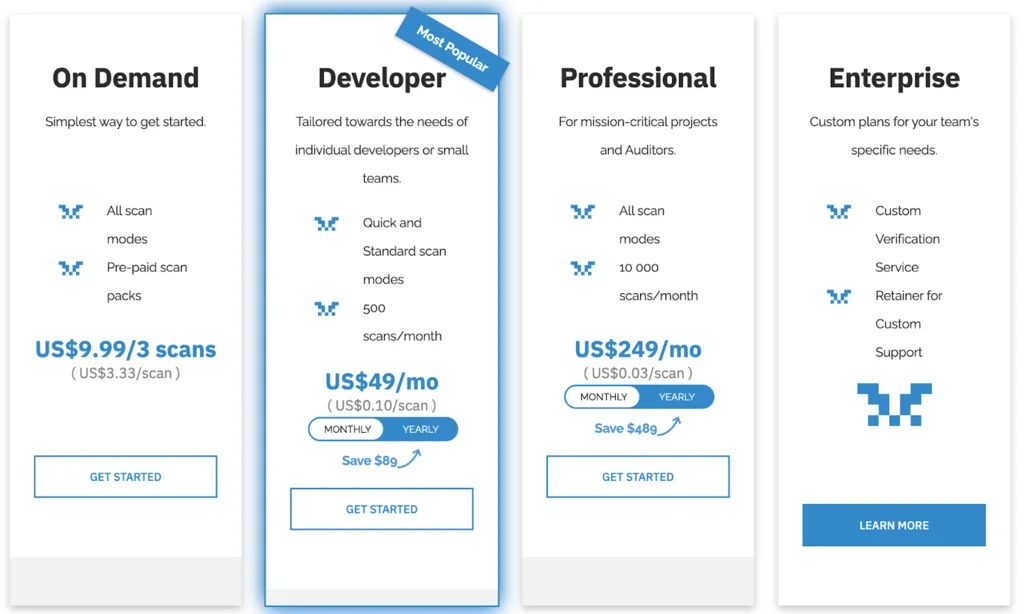
MythX consists of two main parts – web UI and CLI. First, you should select and purchase one of the existing plans on the official MythX website:
After the payment, MythX CLI should be installed. It can be quickly done by running pip3 install mythx-cli or building the project from the source:
- Clone the public repository with git clone https://github.com/dmuhs/mythx-cli
- Install with python3 setup.py install
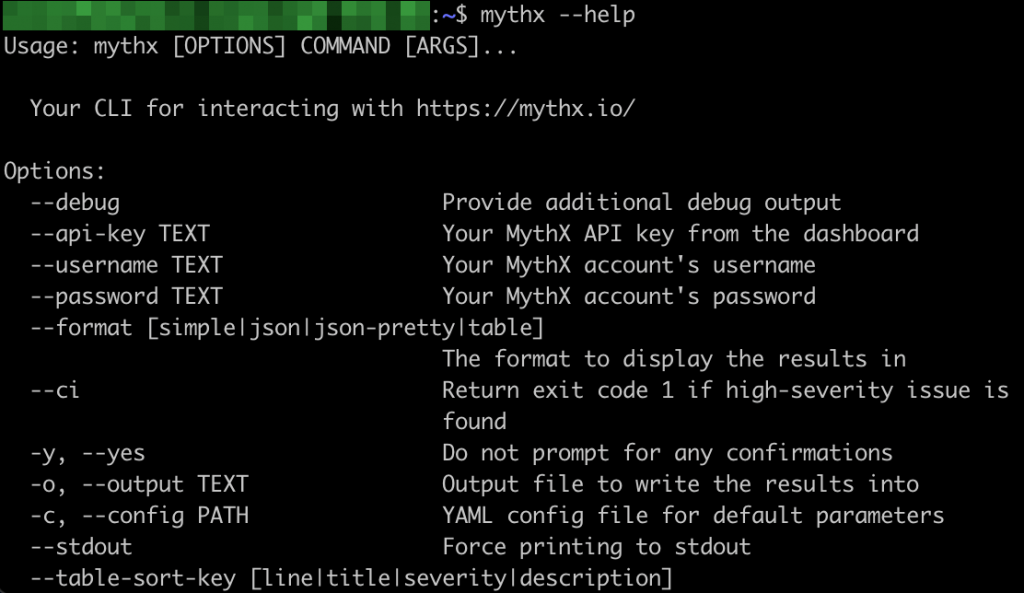
Successful installation may be checked with mythx –help. You should see usage instructions as a result of the execution of the mentioned command.
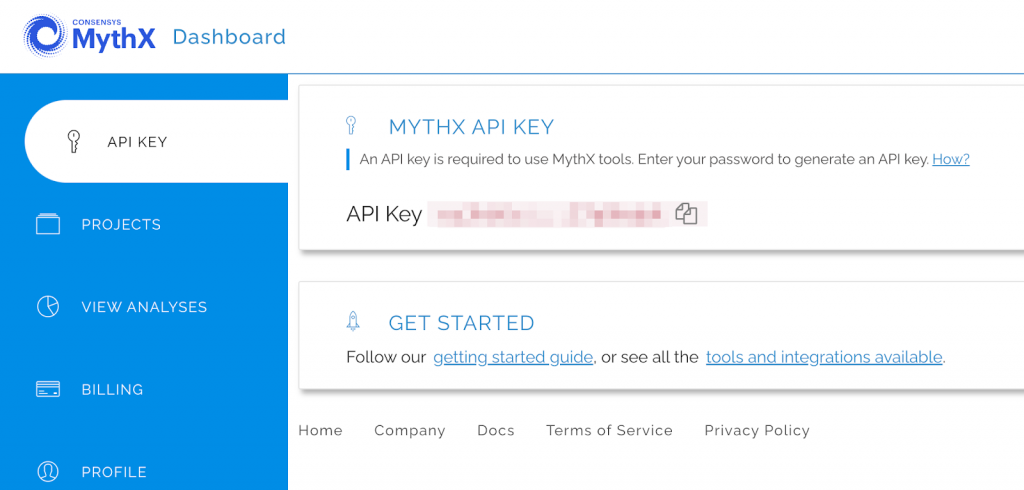
After the purchase and installation of MythX CLI, navigate to https://dashboard.mythx.io/#/console to discover API key which is required for running the scan. To generate and view the key, the password from your account should be entered.
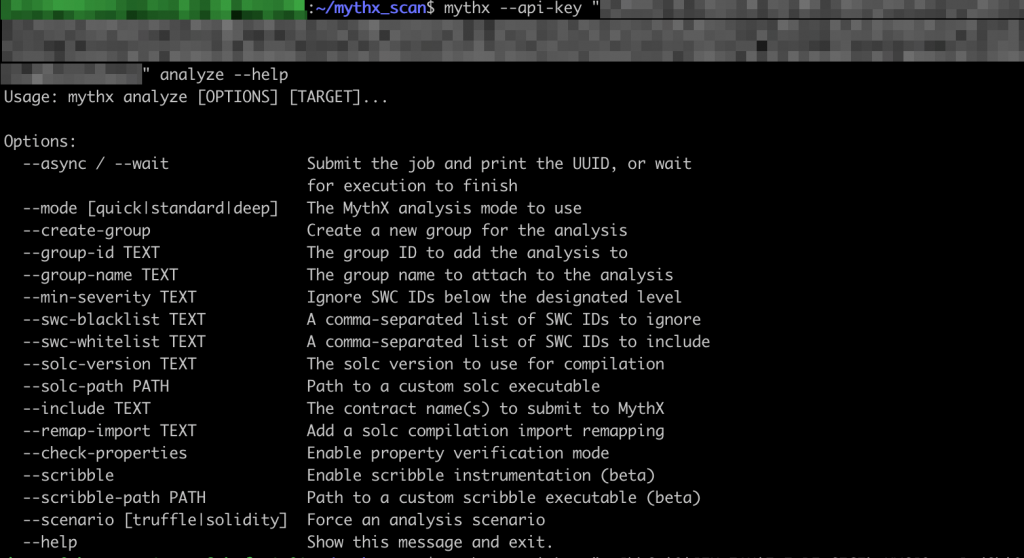
Now we can discover all the possible scan modes with running mythx –api-key “your_api_key” analyze –help.
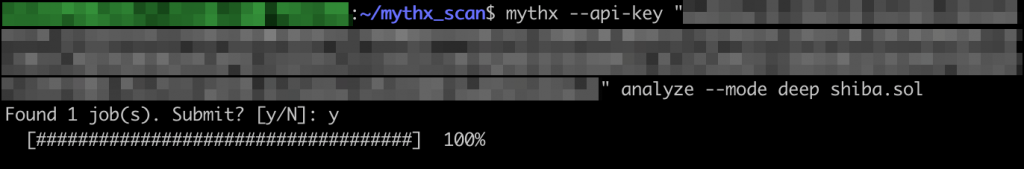
To start fully automatic smart contract analysis in a deep mode, run mythx –api-key “your_api_key”, but be prepared, according to MythX official documentation, the deep scan may take up to one hour and a half.
After the scan, we can navigate to MythX dashboard to check the detailed report with scan results. In our case, the contract appeared well secured, as MythX found only four Low severity issues.
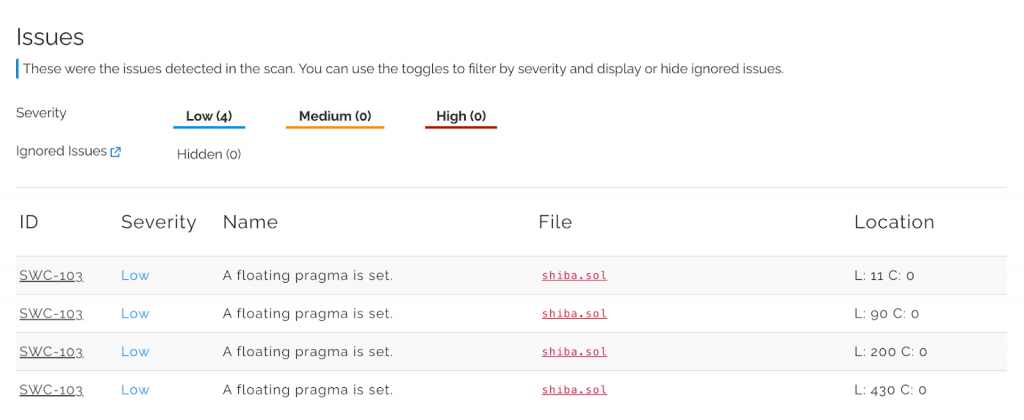
The dashboard interface provides information about the Severity level, location of the issue, and even the corresponding issue ID from SWC registry.
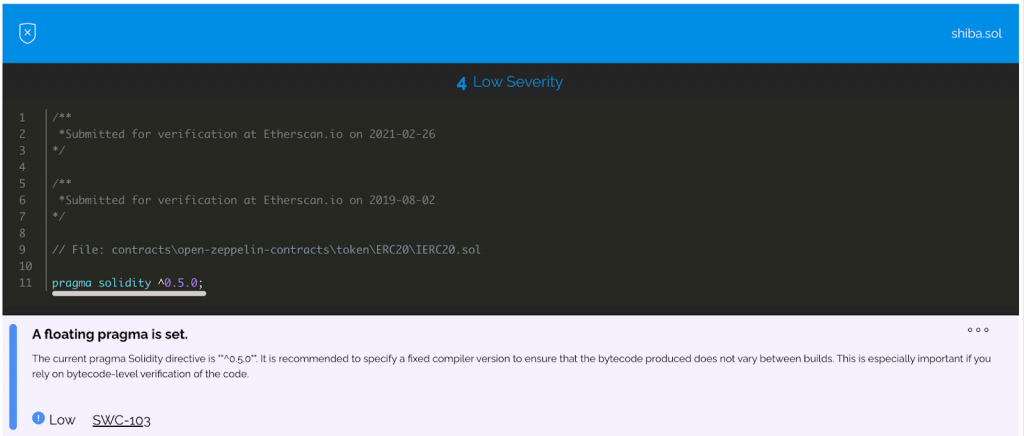
In a more detailed view, MythX provides a vulnerable sample of code and recommendations for how the vulnerability may be fixed.
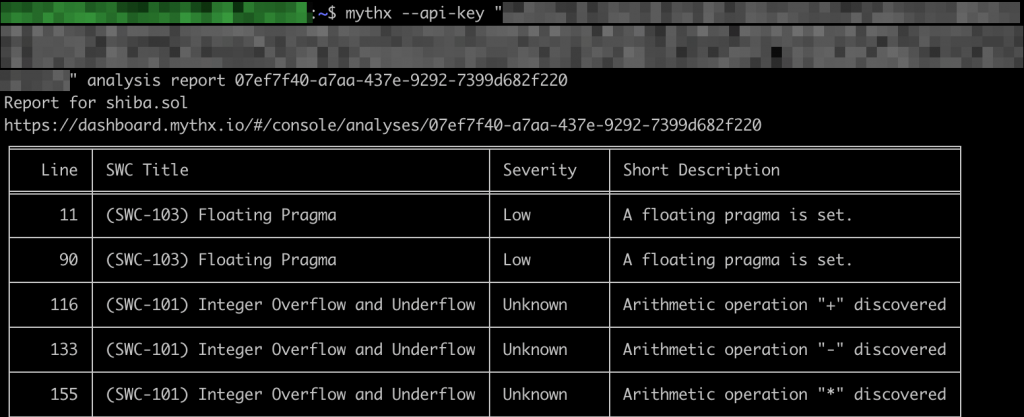
Brief information about scan results also may be viewed through the CLI with mythx –api-key “your_api_key” analysis report your_report_id.
That’s all for now. In this article, we reviewed how to run a deep scan mode and discover a wide range of security flaws in EVM-based Solidity smart contracts. This valuable brand-new skill definitely should be tested on our public smart contract programs to find valid bugs with a high bounty for them. But keep in mind that reports without a detailed Proof of Concept are out of scope, so do not forget to attach the PoC to your report.

